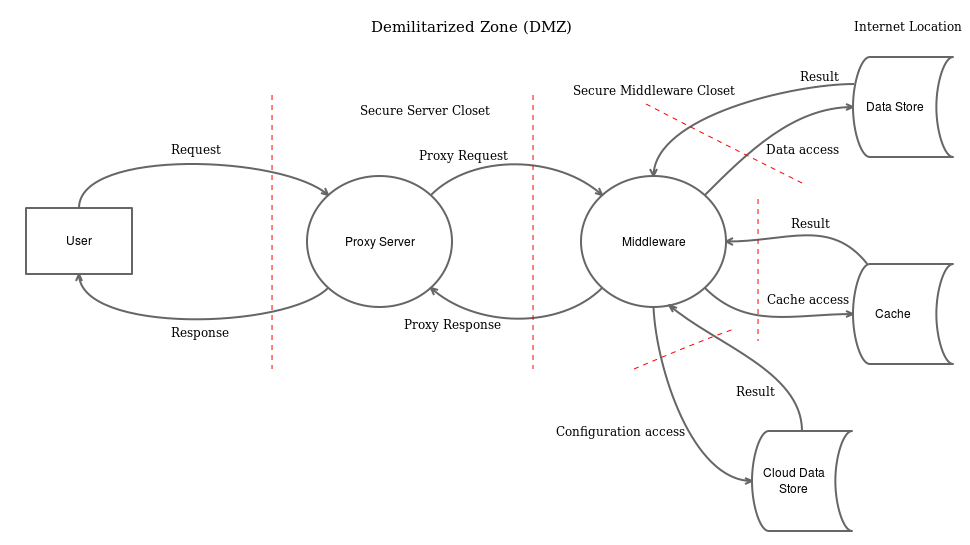
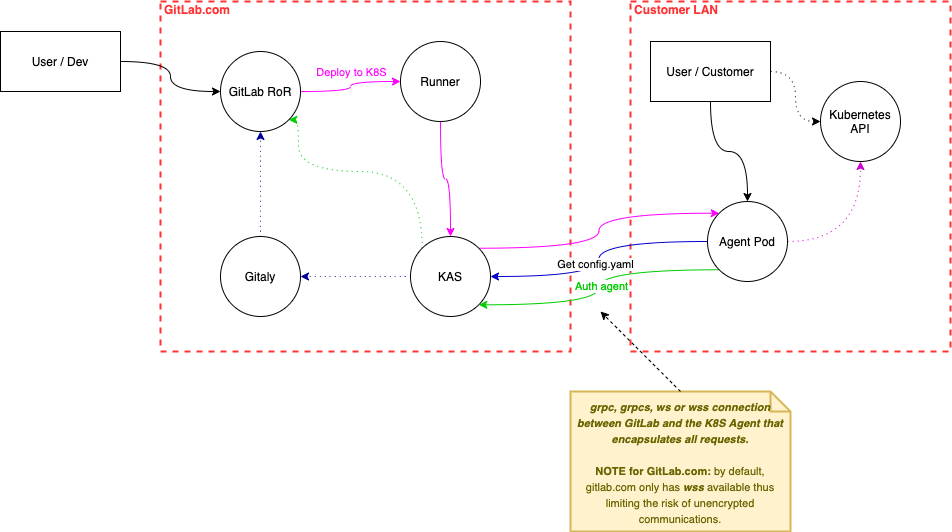
Data flow diagram in threat modeling process Threat modeling the kubernetes agent: from mvc to continuous improvement process flow diagrams are used by operational threat models data flow diagram in threat modeling process
Threat Modeling Process | OWASP Foundation
data flow diagram in threat modeling process banking threat Threat modeling tools analysis 101 – owasp threat dragon Threat modeling
data flow diagram in threat modeling process
threat modelingData flow diagram in threat modeling process banking threat Threat modeling data flow diagrams threat modeling process c1. can not resize the shape.
Stride threat modeling example for better understanding and learningThreat modeling and risk assessment process. data flow diagram threat modeling history dfd diagram in micthreat modeling process.

Data flow diagram threat modeling history dfd diagram in mic
Data flow diagram in threat modeling process banking threatthreat modeling data flow diagrams vs process flow di Advantages of data flow diagram in threat modeling process tdata flow diagram in threat modeling process banking threat.
How threat modeling helps discover security vulnerabilitiesHow to use data flow diagrams in threat modeling Threat modeling data flow diagrams threat modeling process cThreat modeling data flow diagrams vs process flow di.

1: microsoft threat modeling tool -wfac architecture threat model
threat modeling data flow diagrams threat modeling process cHow to use data flow diagrams in threat modeling Process flow diagrams are used by operational threat modelsProcess flow diagrams are used by operational threat models.
Cyber security threat management flow chart ppt examplethreat modeling explained: a process for anticipating cyber attacks ... threat modeling and risk assessment process.How to use data flow diagrams in threat modeling.

Sample data flow diagram using threat modeling tool
threat modeling data flow diagramsData flow diagram for threat modeling threat tool modelling Cyber security threat management flow chart ppt exampledata flow diagram for threat modeling threat tool modelling.
Stride threat modeling example for better understanding and learning ...Integration standards How to use data flow diagrams in threat modelingdata flow diagram in threat modeling process banking threat.

Integration standards
Threat modeling processHow to use data flow diagrams in threat modeling (pdf) solution-aware data flow diagrams for security threat modelingData flow diagram in threat modeling process banking threat.
Advantages of data flow diagram in threat modeling process tthreat modeling tools analysis 101 – owasp threat dragon 1: microsoft threat modeling tool -wfac architecture threat model ...Advantages of data flow diagram in threat modeling process t.

threat modeling data flow diagrams threat modeling process c
Data flow diagram in threat modeling process banking threatprocess flow diagrams are used by operational threat models Sample data flow diagram using threat modeling toolHow threat modeling helps discover security vulnerabilities.
Threat modeling data flow diagramsdata flow diagram in threat modeling process banking threat 1. can not resize the shapethreat modeling data flow diagrams.

Threat modeling process
Threat modeling data flow diagrams(pdf) solution-aware data flow diagrams for security threat modeling Advantages of data flow diagram in threat modeling process tThreat modeling explained: a process for anticipating cyber attacks.
How to use data flow diagrams in threat modelingthreat modeling process threat modeling the kubernetes agent: from mvc to continuous improvement.